Software dependency upgrades
2020.03.05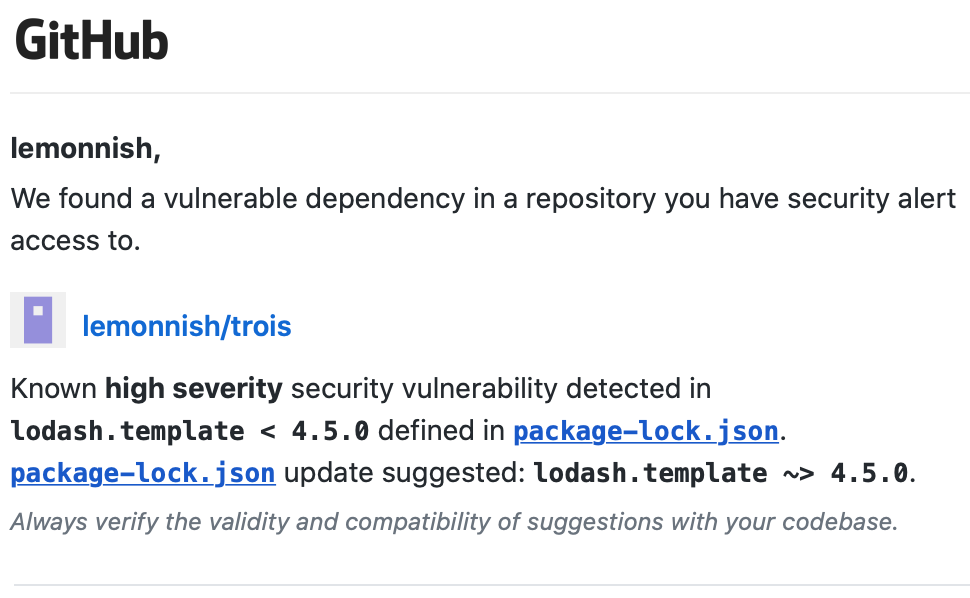
Over the past couple of years, I’ve created a number of websites using various tools. Some are personal projects I developed in order to teach myself new skills. Others are production websites with active traffic that I’ve built to publish my activities and sell products to customers (in addition to being an engineer and sometimes web-developer, I am an artist and printmaker). It seems to be the nature of software, especially web software, that everything develops vulnerabilities and need periodic updates. And the longer you leave the upgrade, the more difficult it is to complete.
This is less of a cohesive writeup, and more of a series of notes for myself the next time I need to upgrade my software dependencies to fix vulnerabilities.
JavaScript
JavaScript is a programming language that can be run in web browsers.
I completed my first JavaScript app, Trois, in September 2018 and wrote about it here. Trois is implemented in React, a popular JavaScript library created by Facebook that can be used to build interactive websites that run in the visitor’s browser.
The command line tool npm is a package manager for installing JavaScript libraries; I used it to install React. npm comes with many commands for keeping your software up to date.
npm auditproduces a list of known security vulnerabilities in all packages and their dependencies (this is a similar list to what Github compiles). The command also gives helpful instructions about steps to take to address those dependencies.npm audit fixcan address most vulnerabilities by checking for and then installing compatible dependency upgrades.
Ruby on Rails
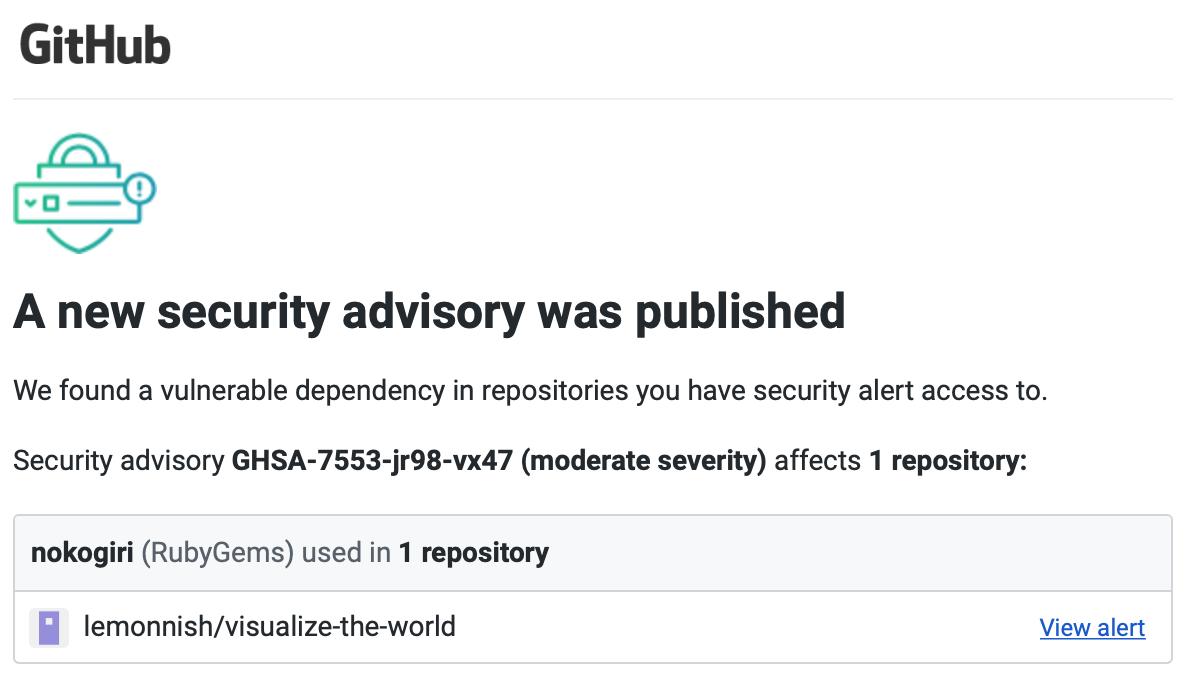
Ruby on Rails is a framework for building interactive websites that run on backend servers. In April 2018 I finished Visualize the World, my first Ruby on Rails application. I wrote about it here.
Compared to Trois, this site was more difficult to upgrade. My difficulties were partly due to the fact that I last looked at the code two years ago and haven’t worked on a Rails application since then.
I started on Rails version 5.1.2 which was released in June 2017. As of writing, the newest Rails release is 6.0.2.1. There were a large number of changes made between the 5.x and 6.x releases, so instead of upgrading to the most recent version of Rails, I upgraded halfway to the last 5.x release: 5.2.4.1. This was enough of an update to resolve all published security vulnerabilities for now.
For the most part, I followed the instructions in the Ruby on Rails guide. However, here are some other notes and resources that I used:
- Use
rails app:updateto get a walkthrough of all code with suggested version-compatible changes (more details) - Use
bundle outdatedto get a list of all installed gems that have newer releases available (Bundler documentation). I cycled through a series of commands to upgrade all outdated dependencies, while making sure they were compatible with my chosen Rails version:- run
bundle outdatedto get recommended gem versions - edit Gemfile.json with new version numbers
- run
bundle updateto install new versions (if this didn’t work, I would revert/modify my Gemfile.json edits) - run
rails testorrails serverto make sure that nothing was broken.
- run
Deploying my changes went smoothly. I previously set up a Heroku pipeline to connect my GitHub repository to Heroku: Heroku automatically deploys the new version when I update code in the master branch.
Jekyll
I built my personal website (including my online print shop) using Jekyll. Read more about it here.
Jekyll is a static site generator built in Ruby; as Ruby versions get upgraded to add features or fix bugs, so too does Jekyll. I started this site using Jekyll 3.7.3; the most recent version as of this writing is 4.0.0.
I updated my Gemfile to request the latest 3.x Jekyll gem (gem "jekyll", "~> 3.7" requests the latest version of Jekyll that is later or equal to 3.7, but earlier than 4.0). In the terminal, I ran bundle outdated to check for outdated gems, then used bundle update to update all gems and dependencies to use the latest versions compatible with the Jekyll version.
Keeping your software up to date is a lot of work, but it’s a necessary security precaution. Plus, periodically updating keeps you safe from all the GitHub email notifications.